The file seems to be structured in a simple text format, with each entry separated by a newline character. The contents might resemble a list of IP addresses, domain names, or other network-related information.
That being said, I can create a fictional piece that might resemble what you're looking for: GERMANY_DATABASE_HQ_FRESH_COMBOLIST.txt
Here's a fictional representation of what some entries in the file might look like: The file seems to be structured in a
This text file appears to be a database extract from a high-security facility in Germany, likely a headquarters (HQ) for a large organization. The file contains a list of fresh combolist data, which could be related to cybersecurity, threat intelligence, or network security. The file contains a list of fresh combolist
The "GERMANY_DATABASE_HQ_FRESH_COMBOLIST.txt" file appears to be a sensitive piece of information, potentially used by a large organization in Germany to monitor and respond to cybersecurity threats. Its contents and purpose are speculative, but it could play a critical role in maintaining the organization's network security and threat intelligence efforts.
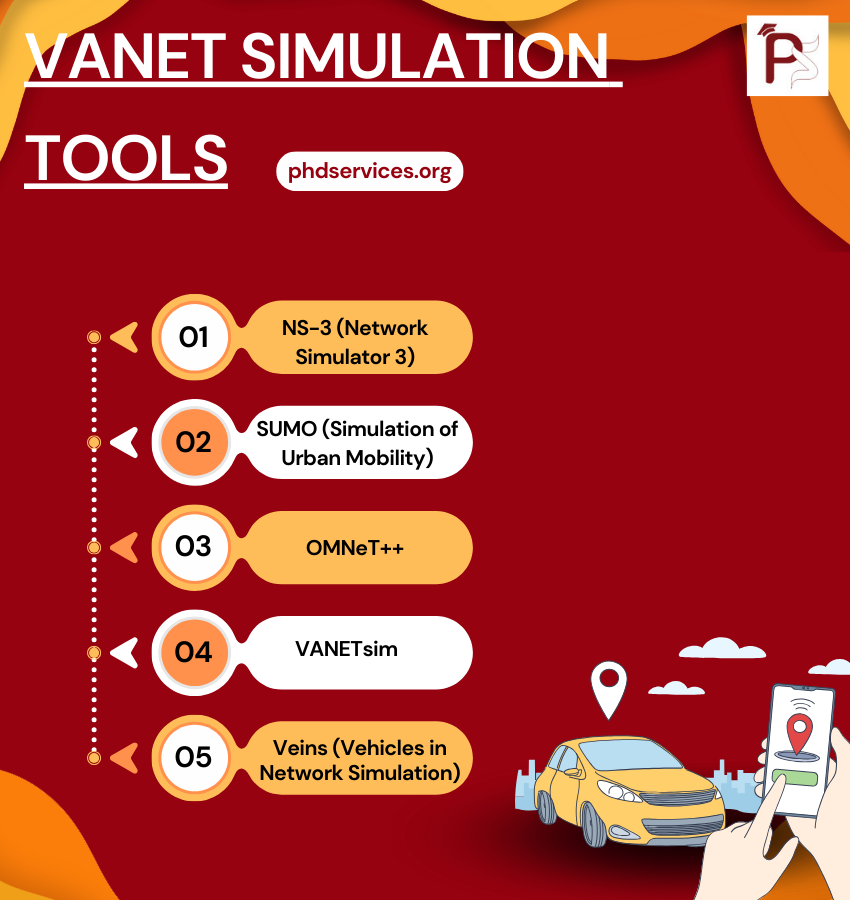
VANET Simulation Tools Topics & Ideas
We utilize cutting-edge VANET Simulation Tools according to your proposed concept. Explore the various Topics & Ideas that are being explored by phdswervices.org. It is common for research students to make mistakes in certain areas, and that is why we offer the guidance of our writers. We ensure that your topic is properly framed with appropriate keywords to enhance its effectiveness.
- Road traffic and geography topology based opportunistic routing for VANETs
- Cooperative pseudonym change scheme based on the number of neighbors in VANETs
- Boosting named data networking for data dissemination in urban VANET scenarios
- VANET Based Vehicle Tracking Module for Safe and Efficient Road Transportation System
- Design and performance evaluation of a PMIPv6 solution for geonetworking-based VANETs
- SEGM: A secure group management framework in integrated VANET-cellular networks
- Secure and privacy-aware traffic information as a service in VANET-based clouds
- A cross layer approach for efficient multimedia data dissemination in VANETs
- Reliability and energy-efficiency analysis of safety message broadcast in VANETs
- Asking neighbors a favor: Cooperative video retrieval using cellular networks in VANETs
- Intelligent Adjustment Forwarding: A compromise between end-to-end and hop-by-hop transmissions in VANET environments
- Performance analysis and implementation of proposed mechanism for detection and prevention of security attacks in routing protocols of vehicular ad-hoc network (VANET)
- A lightweight authentication and privacy-preserving scheme for VANETs using TESLA and Bloom Filters
- LIAP: A local identity-based anonymous message authentication protocol in VANETs
- Practical secure and privacy-preserving scheme for value-added applications in VANETs
- The insights of message delivery delay in VANETs with a bidirectional traffic model
- Nexthop selection mechanism for nodes with heterogeneous transmission range in VANETs
- QualityScan scheme for load balancing efficiency in vehicular ad hoc networks (VANETs)
- A mobility-based scheme for dynamic clustering in vehicular ad-hoc networks (VANETs)
- Regression based critical information aggregation and dissemination in VANETs: A cognitive agent approach